Wolverine Access Vulnerability
Sunday, July 25, 2004
While arranging my class schedule at the University of Michigan, I discovered a vulnerability in Wolverine Access that allowed unrestricted access to the social security numbers, names, and addresses of every student in the University including recent alumni.
Introduction
Wolverine Access (WA) is the University of Michigan\’s online records and registration system. It handles academic, financial, employment, and personal information of students, faculty, and staff. It is based on PeopleSoft software and maintained by MAIS. Most students utilize WA for class registration, financial information, and other academic resources.
Discovery
While arranging my schedule for the fall semester on WA, I attempted to use Mozilla Firefox\’s \“Open Frame in New Tab\” feature to be able to switch between my current schedule and available classes quickly. Due to WA\’s combination of Javascript and frames, effectively navigating through it is often a pain. After opening the frame in a new tab, I was presented with a navigation bar at the top of the page that I had never seen before on WA:
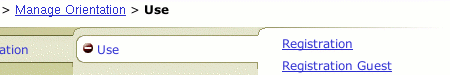
After exploring this previously hidden navigation tree, I came upon \“Registration Guest\“, apparently used for incoming freshmen to register for orientation:
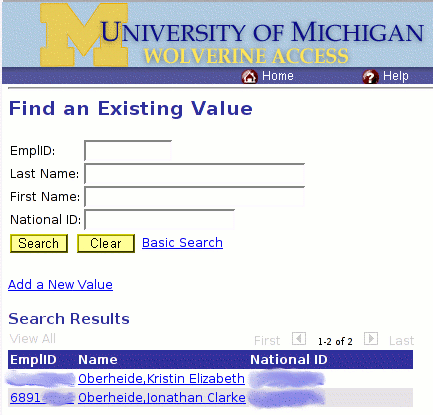
After following this link, I was prompted with a search form with fields EmplID, Last Name, First Name, and National ID. Querying for the last name \“Oberheide\” resulted in the following listing of the personal information of my sister (a recent alum) and I:
Reporting
After discovering the issue, I immediately reported it via email to security\@umich.edu, the UM security incident response team. The next morning I received a call from Jim Knox, Will Rhee, and Liz Sweet, employees of ITCS, and walked them through reproducing the issue. Later in the afternoon, I confirmed the vulnerability was indeed properly fixed. A couple days later, Paul Robinson, of the University Registrar office, sent out a [notice] to all students, notifying them of the incident and of the possibility their information had been accessible to unauthorized parties.
The private information was exposed from February 9th to May 17th, and MAIS has no knowledge of whether the vulnerable area of the site was accessed by any other users. According to University documentation, there were over 54,000 students enrolled in 2004, although the exact number of affected individuals is unknown and could be significantly greater due to the alumni being listed in the database.