Exploiting Live Virtual Machine Migration
Sunday, February 10, 2008
Later this week, I\’ll be presenting at the Black Hat DC Briefings on weaknesses in the security of live virtual machine migration as implemented by popular vendors such as VMware and Xen. I thought I\’d provide a teaser in advance of my presentation detailing some of the topics that will be discussed.
A Trip Down Memory Lane
If you take a look back at the past few years, we\’ve seen a systematic breaking down of isolation boundaries within our computing platforms as new technologies such as virtualization are employed.
We started with physical machines running a single operating system. The state of the machine was protected by hardware mechanisms such as the MMU. However, attacks were still possible against this model, such as physically plugging in a rogue firewire device and DMA\‘ing into physical memory.
As virtualization entered the scene, the state of a machine was no longer protected by hardware, but by a software layer, namely the hypervisor/VMM. As we\’ve seen numerous times, the isolation mechanisms enforced by the hypervisor are often broken due to vulnerabilities in the software, resulting in a VM being able to modify the state of another VM under the same hypervisor.
With the introduction of live migration of virtual machines, we have brought the weakening of isolation boundaries protecting machine state to a whole new level. Using the migration functionality implemented by vendors such as VMware and Xen now exposes the entire machine state of a VM to the network. Now, instead of physical access or access to a VM sharing a hypervisor of the target VM to perform an attack, an attacker simply needs snoop on a network where these migrations are occurring. Exposing this information to the network without authentication or confidentiality guarantees represents a significant security risk.
Exploiting Live Migrations
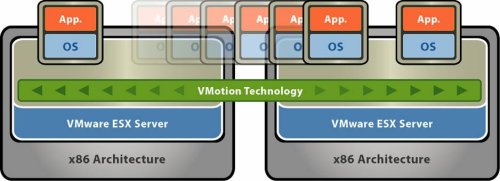
Live migration is an incredibly useful feature and natural extension to virtualization platforms that allows for the transfer of a virtual machine from one physical machine to another with little no or downtime of the services hosted by the virtual machine. To put it simply, a live migration transfers the working state and memory of a virtual machine across the network.
The security of a virtual machine migration hinges on the migration data plane, or the network transit path of which the migration occurs. If this data plane is insecure or unauthentication, an attacker on the network may gain access to the migration, allowing access to the full state of the virtual machine including the operating system kernel, applications and services run within the operating system, and the sensitive data currently being used by those applications. Unfortunately, in both the virtualization offerings by VMware and Xen, insecure migrations are employed allowing an attacker to compromise the integrity of the virtual machines being migrated.
To demonstrate attacks against live migration, we implemented a proof of concept tool called Xensploit. Despite its name, it is effective against both VMware and Xen migrations. During the Black Hat presentation, we will detail several classes of attacks including userspace application exploits, backdoors via kernel manipulation, and virtual machine based rootkits (VMBRs). In addition, we\’ll demonstrate how a VM migration can be manipulated by a malicious party in order to exploit vulnerabilities in the Xen VMM and subvert the hypervisor.
Deployment Risks
The primary goal of my presentation at Black Hat is to raise awareness of these weaknesses in current virtualization offerings from major vendors. IT administrators employing virtualization and live migration functionality need to be aware of the risks associated with such deployments and take the appropriate steps to achieve adequate isolation and secure their infrastructure. Virtualization and, in particular, the live migration of virtual machines represent significant advancements in computing and management capabilities, but much care must be taken to properly implement the appropriate security mechanisms by both the vendors and the enterprises deploying the software.
Materials Update
The materials of my Black Hat presentation are now available:
- Presentation:: /files/blackhat08-migration-pres.pdf
- Whitepaper: /files/blackhat08-migration.pdf